IT Requirements for FINRA Compliance in New York – (UPDATED For 2026)
Beyond Rule 4370: A Cybersecurity and Compliance Guide for Broker-Dealers
Broker-dealers face strict technology and security standards from FINRA that go beyond basic IT management. FINRA compliance IT requirements include specific rules for business continuity planning, cybersecurity protocols, vendor oversight, and customer data protection that firms must follow to avoid regulatory penalties. Understanding these requirements helps your firm build a compliant technology infrastructure.
FINRA Rule 4370 requires all broker-dealers to maintain written business continuity plans and conduct regular testing. The organization also publishes cybersecurity guidelines and assessment tools that set expectations for how firms should protect their systems and client information. These standards cover everything from password policies to penetration testing schedules.
Your firm needs a clear roadmap to meet FINRA's technology requirements. This guide breaks down the essential compliance areas, including vendor management protocols, data protection standards, and the cybersecurity assessment questionnaire. You'll learn what FINRA expects and how to implement the right controls at your broker-dealer firm.
Key Takeaways
- FINRA requires broker-dealers to maintain business continuity plans, implement cybersecurity controls, and protect customer data through specific IT requirements
- Firms must conduct annual penetration testing, complete cybersecurity assessments, and maintain proper oversight of third-party vendors
- Following FINRA's published cybersecurity guidelines and technical safeguards helps broker-dealers avoid regulatory violations and protect client information
Essential FINRA Compliance IT Requirements for Broker-Dealers
Broker-dealers must maintain specific technology controls to protect customer data and ensure business continuity. FINRA sets minimum standards for cybersecurity practices, vendor oversight, and system resilience that apply to firms of all sizes.
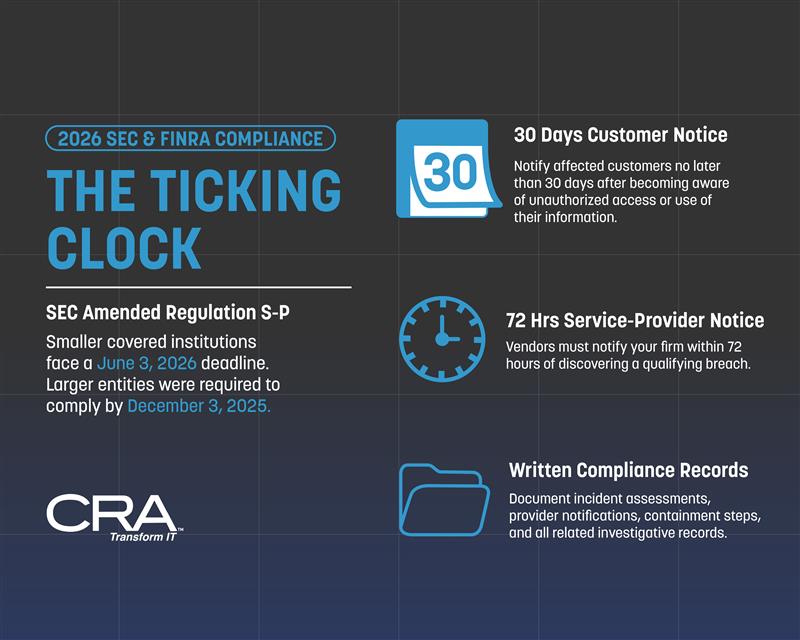
REMINDER! - 2026 Compliance Alert: The Regulation S-P "Ticking Clock"
As of March 2026, the June 3, 2026 compliance date for smaller covered institutions under the SEC’s amended Regulation S-P is approaching. Larger entities were required to comply by December 3, 2025.
Under the amended rule, covered institutions must maintain a written incident response program designed to detect, respond to, and recover from unauthorized access to or use of customer information. The rule also requires:
- Customer notice within 30 days: Notice must be provided as soon as practicable, but no later than 30 days after the firm becomes aware that unauthorized access to or use of customer information has occurred or is reasonably likely to have occurred.
• Service-provider notice within 72 hours: Policies and procedures must be reasonably designed to ensure service providers notify the firm as soon as possible, but no later than 72 hours after the provider becomes aware of a qualifying breach.
• Written compliance records: Firms must maintain records documenting compliance, including incident assessments, provider notifications, containment steps, and related investigative records.
Firms should confirm that their governance, vendor oversight, and incident-handling workflows can meet these deadlines.
Does your current IT stack support these time-sensitive mandates? If not, the time to bridge the gap is now.
Overview of FINRA's Technology Standards
In 2026, FINRA’s technology standards have evolved from "static" check-the-box compliance to a model of active, continuous oversight. The regulatory landscape is no longer just about firewalls; it is centered on protecting customer information against AI-driven threats and ensuring high-velocity operational resilience.
The core requirements draw from three primary regulatory engines: FINRA Rule 4370 for business continuity, the SEC’s amended Regulation S-P for data protection, and the newly released 2026 FINRA Annual Regulatory Oversight Report, which serves as the current enforcement roadmap.
The "Ticking Clock": Regulation S-P & June 2026
The most urgent priority for broker-dealers right now is the June 3, 2026, compliance deadline for the Regulation S-P amendments. While larger firms met this in late 2025, smaller entities are now under a strict mandate to operationalize:
- Incident Response Programs: You must have written policies to detect, respond to, and recover from unauthorized access.
- 30-Day Notification Rule: Firms are now required to provide written notice to affected individuals as soon as practicable, but no later than 30 days after becoming aware of a breach.
Beyond the 2015 Framework: The 2026 Oversight Shift
While the 2015 Report on Cybersecurity Practices was once the gold standard, it has been superseded by the 2026 Annual Regulatory Oversight Report. This new framework focuses on "New for 2026" risks that examiners are prioritizing in current audits:
- Generative AI & AI Agents: FINRA now expects "human-in-the-loop" protocols for any AI-assisted customer communications and "explainability" for autonomous AI agents.
- Cyber-Enabled Fraud: Active monitoring is required for deepfake audio/video, "quishing" (QR code phishing), and polymorphic malware that traditional antivirus often misses.
- Active Vendor Due Diligence: You are now expected to audit not just your vendors, but their "sub-processors" and any hidden AI integrations within their tech stacks.
Failing to update your technology controls to match these 2026 standards doesn't just result in "deficiency letters"—it leaves your firm vulnerable to the sophisticated, AI-powered exploits currently targeting the NYC financial sector.
Regulatory Scope and Applicability
All FINRA member firms must comply with technology requirements regardless of size or business model. The specific controls you implement should match your firm's risk profile, customer base, and technology footprint.
Introducing broker-dealers face the same obligations as self-clearing firms, though your approach may differ based on services your clearing firm provides. You remain responsible for vendor oversight even when third parties host your systems.
FINRA Rule 4370 requires business continuity plans from every member firm. Rule 3110 mandates supervision of electronic communications and trading systems. Regulation S-P applies to all firms handling customer information.
Core Compliance Obligations for IT Systems
Your IT systems must include technical controls that prevent unauthorized access to customer data and trading platforms. These controls include:
- Multi-factor authentication for remote access and sensitive systems
- Encryption for data at rest and in transit
- Network segmentation to isolate critical systems
- Patch management processes for operating systems and applications
- Antivirus and anti-malware protection on all endpoints
You must conduct annual penetration testing to identify security weaknesses before attackers exploit them. This testing should cover both external and internal threats to your network.
Your business continuity plan needs specific technology components. You must identify alternate physical locations for operations and document how you'll restore critical systems within recovery time objectives. FINRA expects you to test these plans annually.
Access controls require regular review. You should revoke system access immediately when employees leave and conduct quarterly audits of user permissions. Privileged accounts need additional monitoring and logging.
FINRA Rule 4370: Business Continuity and Disaster Recovery
FINRA Rule 4370 requires broker-dealers to create and maintain written business continuity plans that address data backup, recovery time objectives, and alternate physical locations for operations. These plans must be updated annually and made available to customers upon request.
Key Provisions of Rule 4370
Rule 4370 mandates that your firm's business continuity plan must identify procedures for emergency or significant business disruptions. You need to document how your firm will continue operations if a disaster affects your primary business location.
Your plan must address several critical elements. These include data backup and recovery, financial and operational assessments, alternate communications with customers and employees, and alternate physical location of employees.
You must designate emergency contacts and create a plan to recover and resume operations quickly. The rule requires annual reviews and updates to your business continuity plan based on material changes to your operations, structure, business, or location.
FINRA requires you to disclose your business continuity plan summary to customers at account opening. You also need to post the summary on your website if you maintain one for business purposes. The summary should explain your continuity and recovery plan in clear terms that customers can understand.
IT System Redundancy and Data Backup
Your firm must establish redundant systems to protect critical business data and applications. This means maintaining backup servers, duplicate databases, and alternative network infrastructure that can activate if primary systems fail.
You need to store backup data at a separate geographic location from your main operations. Your backup site should be far enough away to avoid the same regional disaster that might affect your primary location.
Critical backup requirements include:
- Daily incremental backups of all transaction data
- Weekly full system backups
- Off-site storage of backup media
- Regular testing of data restoration procedures
- Documentation of backup schedules and retention policies
Your recovery time objective (RTO) and recovery point objective (RPO) must align with your business needs. Most broker-dealers aim for an RTO of 4-24 hours and an RPO that minimizes data loss to the previous business day or less.
Crisis Communication Protocols
You must establish clear communication channels to reach employees, customers, and regulators during a disruption. Your plan should include multiple contact methods since traditional phone lines or email systems may be unavailable during a crisis.
Your crisis communication plan needs to identify specific individuals responsible for contacting different groups. You should maintain updated contact lists for all employees, critical customers, service providers, and regulatory bodies.
Essential communication elements include:
- Primary and backup phone numbers for key personnel
- Email distribution lists for mass notifications
- Text message alert systems
- Alternative communication platforms (such as web portals or social media)
- Scripts or templates for customer notifications
You need to test your communication protocols regularly to confirm they work when needed. Your employees should know how to access emergency contact information and understand their responsibilities during a disruption. FINRA expects you to communicate with affected customers promptly about how the disruption impacts their accounts and when normal operations will resume.
FINRA Cybersecurity Checklist: Implementation and Best Practices
FINRA compliance IT requirements include specific security controls that protect customer data and firm operations. Your implementation must address access controls, continuous monitoring systems, and documented response procedures.
Mandatory Controls and Procedures
You must implement written policies that cover all aspects of your cybersecurity program. FINRA expects you to maintain current documentation that describes your security controls, data protection methods, and employee responsibilities.
Your firm needs to conduct regular risk assessments that identify vulnerabilities in your systems. These assessments should happen at least annually, with updates whenever you add new technology or services.
Required documentation includes:
- Written cybersecurity policies and procedures
- Risk assessment reports and findings
- Employee training records and acknowledgments
- Vendor security review documentation
- Audit logs and security event records
You must establish data encryption standards for customer information both in transit and at rest. Your policies should specify encryption requirements for emails, file transfers, and database storage.
Employee training programs need to run at least annually. Your training must cover phishing awareness, password security, social engineering tactics, and proper handling of customer data.
Access Management and Monitoring
You need to implement role-based access controls that limit system access to only what each employee requires for their job. Your access management system should include multi-factor authentication for all remote access and privileged accounts.
Key access control requirements:
- Multi-factor authentication for remote access
- Regular review of user permissions and access rights
- Immediate termination of access for departing employees
- Separate administrator accounts from regular user accounts
- Password complexity requirements and rotation policies
Your monitoring systems must track user activity and flag suspicious behavior. You should review access logs regularly to identify unauthorized attempts or unusual patterns.
Privileged accounts require additional oversight. You need to maintain detailed logs of all administrative actions and conduct quarterly reviews of these high-level permissions.
Incident Response Preparedness
Your incident response plan must include specific steps for detecting, containing, and recovering from security breaches. You need to identify your response team members and document their contact information and responsibilities.
You must establish clear escalation procedures that define when to notify senior management, regulators, and affected customers. Your plan should include specific timeframes for each notification requirement.
Your response plan needs:
- Contact information for your response team
- Step-by-step procedures for different incident types
- Evidence preservation and documentation requirements
- Communication templates for internal and external notifications
- Recovery procedures and system restoration steps
Regular testing of your incident response plan helps identify gaps before an actual event occurs. You should conduct tabletop exercises at least annually that simulate different types of security incidents.
Your firm must maintain relationships with external resources such as forensic investigators, legal counsel, and cybersecurity experts. These contacts should be established before an incident occurs so you can respond quickly when needed.
Broker-Dealer IT Security: Technical Safeguards
Broker-dealers must implement specific technical controls to protect their systems and customer data. These safeguards include network protections, device security measures, and cloud-based system controls.
Network Security Architectures
Your firm needs to segment its network into different zones based on data sensitivity and user access levels. This means separating trading systems from back-office operations and creating isolated segments for high-risk areas.
Core network security requirements include:
- Firewalls at network boundaries and between internal segments
- Intrusion detection and prevention systems (IDS/IPS)
- Virtual private networks (VPNs) for remote access
- Network access control (NAC) to verify device compliance
You should implement a zero-trust architecture that verifies every access request. This approach assumes no user or device is trustworthy by default, even inside your network perimeter.
Your network must include monitoring tools that track traffic patterns and flag suspicious activity. These systems should log all access attempts and maintain records for at least six years to meet FINRA requirements.
Endpoint Protection Strategies
Every device that accesses your systems needs protection against malware and unauthorized access. This includes workstations, laptops, mobile devices, and servers used by your employees.
Your endpoint security must include:
- Anti-malware software with real-time scanning and automatic updates
- Disk encryption for all devices that store or access customer data
- Multi-factor authentication for system access
- Mobile device management (MDM) for smartphones and tablets
- Application whitelisting to prevent unauthorized software execution
You need to patch all devices within 30 days of security updates becoming available. Critical vulnerabilities require faster response times, often within days.
Your firm should disable USB ports and other removable media on devices that access sensitive systems. If you allow removable media, you must scan all devices before use and maintain detailed logs of file transfers.
Cloud Security Considerations
When you use cloud services, you remain responsible for protecting your customer data and meeting FINRA compliance IT requirements. Your vendor agreements must clearly define security responsibilities.
You need to verify that your cloud providers offer:
- Data encryption both in transit and at rest
- Regular security audits and SOC 2 reports
- Geographic data storage controls to meet regulatory requirements
- Access logging and monitoring capabilities
Your cloud access policies should enforce the same authentication standards you use for on-premises systems. This includes multi-factor authentication and role-based access controls that limit what each user can view or modify.
You must conduct your own security assessments of cloud vendors before implementation and annually thereafter. These reviews should verify that the vendor maintains appropriate controls and hasn't changed their security practices.
Vendor Management and Third-Party Risk
FINRA requires broker-dealers to assess and monitor all third-party vendors who access your systems or handle customer data. You must maintain detailed records of vendor relationships and verify their security practices meet regulatory standards.
Vendor Due Diligence Requirements
You need to conduct thorough security assessments before hiring any third-party vendor. FINRA expects you to review vendor cybersecurity policies, incident response plans, and data protection measures.
Your due diligence process must include requests for SOC 2 reports, insurance certificates, and recent security audit results. You should verify that vendors encrypt data in transit and at rest. You must also confirm they have adequate business continuity plans.
Key vendor assessment areas include:
- Data access levels and storage locations
- Security certifications (ISO 27001, SOC 2 Type II)
- Incident response procedures
- Employee background check policies
- Disaster recovery capabilities
- Insurance coverage amounts
You need to document all vendor evaluations in writing. Your records should explain why you approved each vendor and what risks you identified during the review process.
Ongoing Monitoring of Service Providers
You must monitor vendors continuously after the initial approval. FINRA cybersecurity checklist items require annual reviews of all critical service providers at minimum.
Your monitoring program should include quarterly security questionnaires and regular reviews of vendor security incidents. You need to track when vendor certifications expire and request updated documentation.
You should establish clear contract terms that give you the right to audit vendors. Your agreements must specify data handling requirements and breach notification timeframes. Most firms require vendors to notify them within 24 hours of any security incident.
You must reassess vendors whenever they experience a data breach or make significant changes to their services. You should also review vendors when FINRA issues new guidance about third-party risk management.
Customer Data Protection and Privacy Standards
FINRA compliance IT requirements mandate specific technical controls to protect customer information from unauthorized access and breaches. Broker-dealers must implement encryption standards and authentication systems that meet regulatory expectations.
Encryption and Data Loss Prevention
You must encrypt all customer data both at rest and in transit. FINRA expects broker-dealers to use industry-standard encryption protocols like AES-256 for stored data and TLS 1.2 or higher for data transmission.
Your firm needs to deploy data loss prevention (DLP) tools that monitor and block sensitive information from leaving your network. These systems should scan emails, file transfers, and cloud uploads for customer account numbers, Social Security numbers, and other personally identifiable information.
You should maintain an inventory of where customer data lives across your systems. This includes databases, file shares, employee laptops, and mobile devices. Regular scans help you identify unencrypted data that needs protection.
Your encryption key management process must restrict access to authorized personnel only. You need to rotate encryption keys according to your security policy and store them separately from the encrypted data.
Authentication Protocols
You must implement multi-factor authentication (MFA) for all systems that access customer data. FINRA cybersecurity checklist items specifically call out MFA as a critical control for broker dealer IT security.
Your authentication system should require at least two factors: something users know (password), something they have (security token or phone), or something they are (biometric). Password requirements need to enforce minimum length of 12 characters and complexity rules.
You should configure session timeouts that automatically log users out after periods of inactivity. Most firms set this between 15-30 minutes for systems containing customer information.
Your access controls must follow the principle of least privilege. Employees should only access customer data necessary for their specific job functions.
Cybersecurity Assessment and Penetration Testing
FINRA expects broker-dealers to regularly test their security systems and document potential weaknesses. Your firm must conduct annual penetration tests and complete cybersecurity assessments to prove you meet regulatory standards.
Annual Penetration Testing Requirements
FINRA compliance IT requirements include yearly penetration testing to identify vulnerabilities in your systems. You need to hire qualified professionals to attempt controlled attacks on your network, applications, and security controls.
Your penetration tests must cover all critical systems that handle customer data or trading activities. The tests should include both external threats from the internet and internal threats from within your network.
You must document all findings from penetration tests and create remediation plans for discovered vulnerabilities. FINRA expects you to fix high-risk issues promptly and track progress on all security improvements.
Keep detailed records of who performed the tests, what methods they used, and when you completed the work. Your documentation should show the scope of testing, all vulnerabilities found, and how you addressed each problem.
Cybersecurity Assessment Questionnaire
The FINRA cybersecurity checklist requires you to complete regular self-assessments of your security practices. You should evaluate your policies, procedures, and technical controls against industry standards.
Your assessment must review:
- Access controls and authentication methods
- Data encryption for customer information
- Network security and monitoring systems
- Incident response procedures
- Employee training programs
- Vendor security requirements
Document your answers with specific evidence of the controls you have in place. You need to identify gaps in your broker dealer IT security and create action plans to address them.
Ongoing Evaluation and Reporting
You must monitor your cybersecurity program continuously, not just during annual reviews. Your IT team should track security metrics, log analysis, and threat intelligence to spot new risks.
Create regular reports for senior management that show the status of security controls and any incidents that occurred. Your board needs to understand cybersecurity risks and how you're managing them.
Update your assessment after major changes to your technology, new regulations, or significant security events. FINRA Rule 4370 requires you to adapt your security program as threats evolve.
Leveraging FINRA's Report on Cybersecurity Practices
FINRA's Report on Cybersecurity Practices gives you a detailed guide for protecting your firm from cyber threats. The report outlines effective security measures based on industry best practices and real-world examples from broker-dealers.
You can use this report as a benchmark to evaluate your current security setup. It covers four main areas that need your attention:
Key Areas from FINRA's Report:
- Governance and Risk Assessment - How you identify and manage cyber risks across your firm
- Technical Controls - Systems you use to protect networks, data, and devices
- Data Loss Prevention - Methods to stop sensitive information from leaving your firm
- Vendor Management - How you monitor third-party providers who access your systems
The report provides specific examples of security practices that work well. You can compare these practices against your own policies to find gaps.
FINRA expects you to regularly review this report and update your security program. The agency uses these guidelines when examining your firm's cybersecurity during audits.
You should document how your firm addresses each area in the report. This documentation helps during FINRA exams and shows you take cybersecurity seriously.
The report also includes common weaknesses FINRA finds during examinations. Review these problem areas to make sure your firm avoids the same mistakes. You can download the full report from FINRA's website and share it with your IT and compliance teams.
Important Legal Disclaimer
General Information Only: The information provided in this article is for general informational and educational purposes only. It does not constitute legal, financial, or professional compliance advice. While Computer Resources of America strives to ensure the accuracy and timeliness of the information presented as of the publication date, the regulatory landscape—including New York Rules of Professional Conduct, the NY SHIELD Act, and CLE requirements—is subject to frequent change and varying interpretations by courts and ethics committees.
No Professional Relationship: Your use of this website or the information contained in this blog post does not create a professional relationship between you and Computer Resources of America. We are an IT services provider, not a law firm. Compliance with the New York Rules of Professional Conduct is the sole responsibility of the licensed attorney.
Fact-Checking and Accuracy: While we make every effort to provide comprehensive guides, Computer Resources of America makes no representations or warranties of any kind, express or implied, about the completeness, accuracy, or reliability of the information, statistics, or legal citations contained herein. Laws and technical standards in 2026 are evolving rapidly; therefore, any reliance you place on such information is strictly at your own risk.
Limitation of Liability: In no event will Computer Resources of America be liable for any loss or damage, including without limitation, indirect or consequential loss or damage, or any loss or damage whatsoever arising from loss of data, disciplinary actions, or malpractice claims arising out of, or in connection with, the use of this guide.
Consult a Professional: We strongly recommend that NYC law firms consult with their own legal counsel, ethics advisors, or the New York State Bar Association to confirm their specific compliance obligations. Technology implementations should always be tailored to a firm’s unique risk profile by a qualified IT professional.
