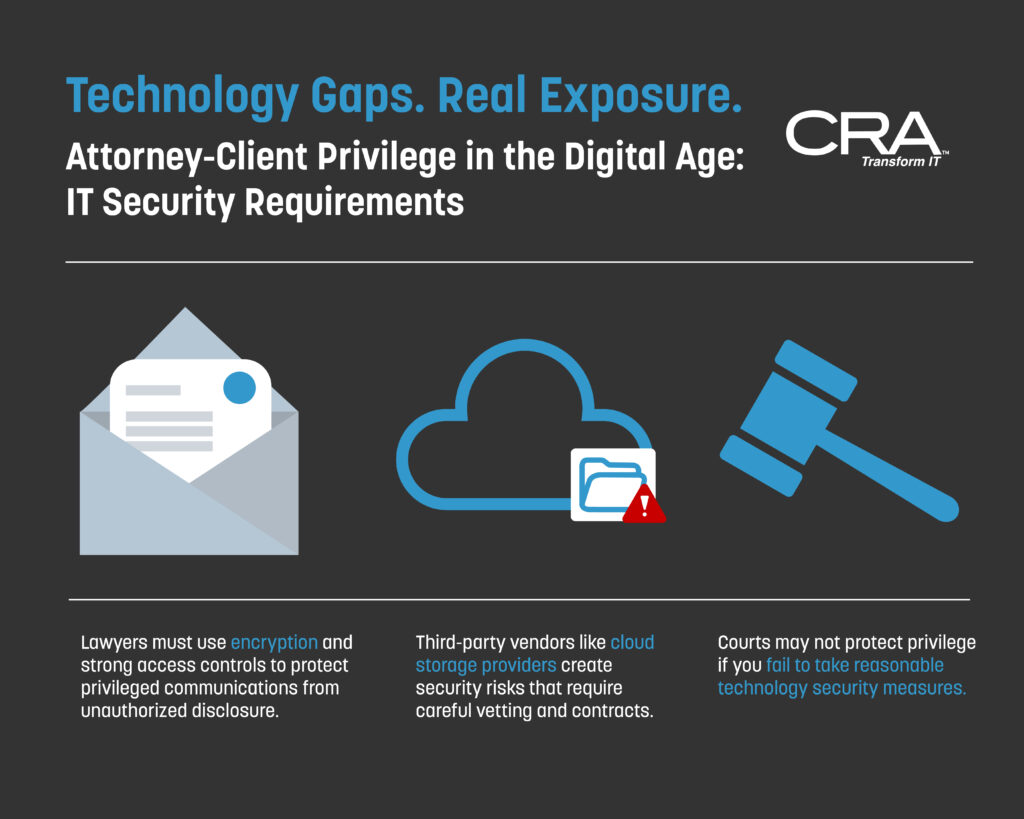
Attorney-Client Privilege IT Security: Modern Protection Strategies
Lawyers have always been required to protect client secrets, but technology has made this job much harder. Attorney client privilege IT security now requires specific technical measures like encryption, access controls, and secure communication systems to meet ethical standards. A single mistake with email, cloud storage, or mobile devices can expose confidential information and put…
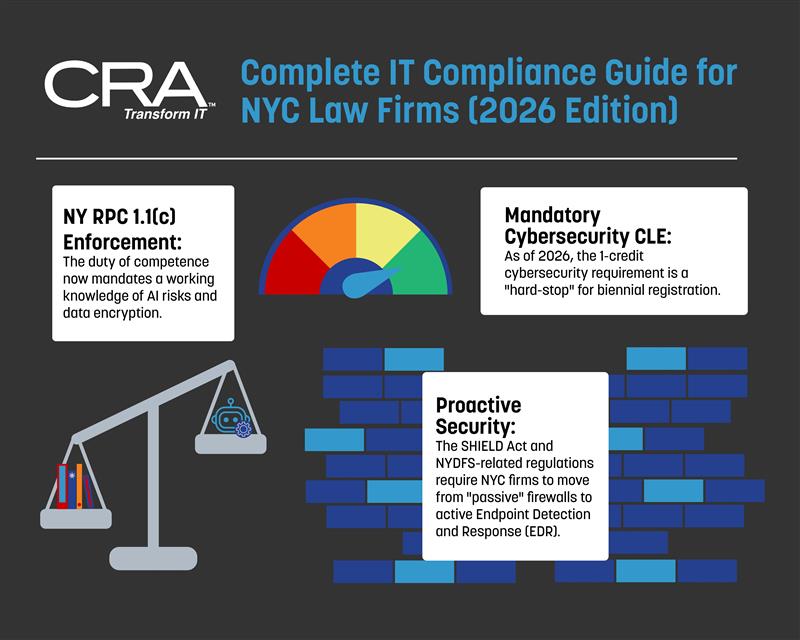
Read MoreComplete IT Compliance Checklist for NYC Law Firms (2026 Edition)
Law firm IT compliance protects your practice from ethical violations, data breaches, and regulatory penalties. NYC law firms face unique technology obligations under state bar rules, grievance committee oversight, and strict cybersecurity regulations. Whether you manage a small practice or a large firm, understanding these requirements is not optional anymore. In 2026, NYC law firms…
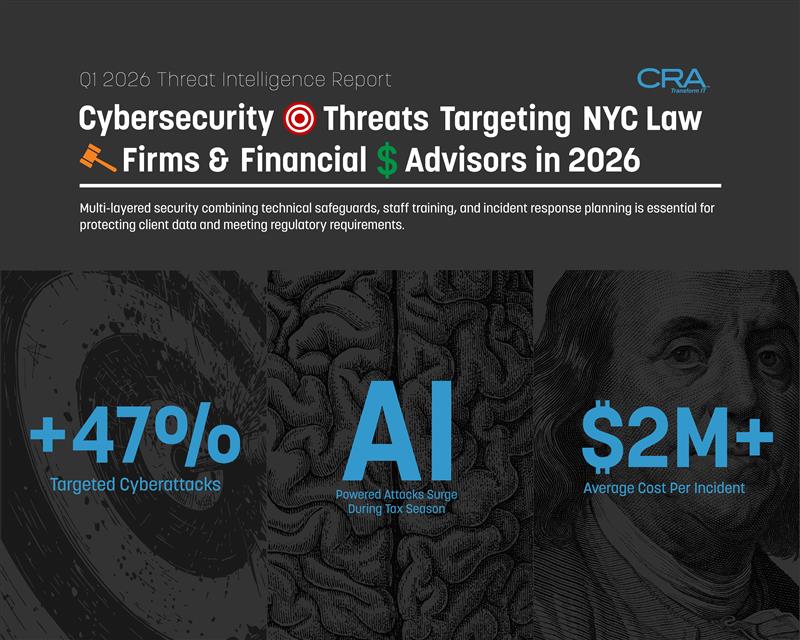
Read MoreQ1 Threat Intelligence Report: Cybersecurity Threats Targeting NYC Law Firms & Financial Advisors in 2026
Law firms and financial advisors in New York City are facing their most dangerous quarter yet. In the first six weeks of 2026, cybercriminals launched targeted attacks against professional services firms at rates 47% higher than the same period last year, with average ransom demands reaching $2.3 million for law firms and breach costs averaging…
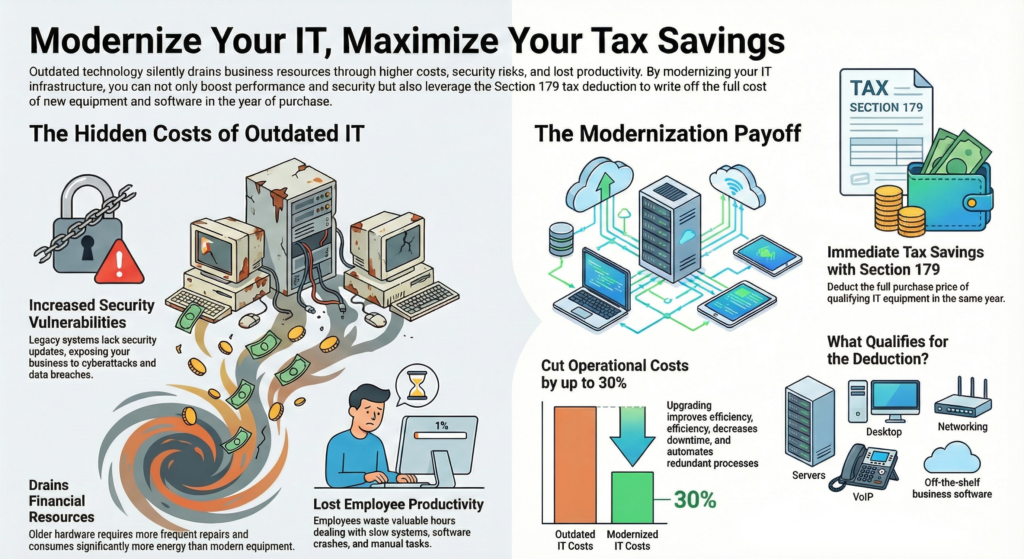
Read MoreGive Yourself the Gift of Modernizing Your IT Infrastructure: Lower Your Tax Bill with Section 179
Your business could save thousands of dollars this tax season while upgrading the technology that keeps your operations running. Section 179 lets businesses deduct the full purchase price of qualifying IT equipment and software in the year of purchase, turning necessary upgrades into immediate tax savings. Many companies continue using outdated hardware and software without…
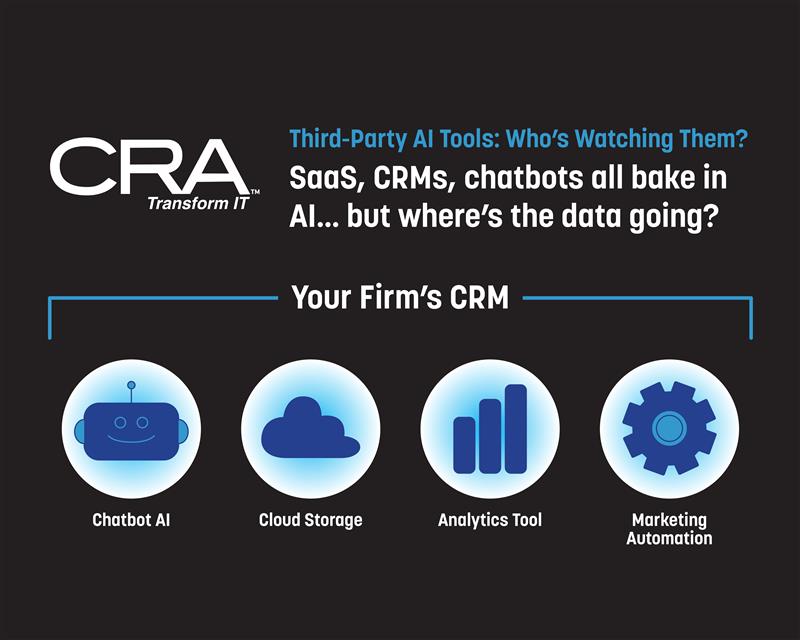
Read MoreThird-Party AI Tools: Who’s Watching Them? SaaS, CRMs & Chatbot Data Risks
Your client data may already be leaving the building without your knowledge. Modern SaaS platforms, CRMs, and chatbots now integrate AI features that can automatically share sensitive information with third-party vendors. While these tools promise better customer insights and automated responses, they often send data to unknown locations with unclear storage practices. The biggest risk…
Read MoreSecuring Financial AI from Attacks
Model Poisoning & Manipulation What if your fraud detection system started letting fraud through? This nightmare scenario becomes reality when attackers use model poisoning to corrupt AI systems that protect financial institutions. Attackers can manipulate AI models by injecting bad data during training or using adversarial inputs that fool the system into making wrong decisions.…
Read MoreAI-Powered Phishing
Machine-Learned Deception in Cybersecurity Would your staff spot a fake if it looked better than the real thing? Cybersecurity professionals now face a new reality where AI-powered phishing attacks create perfect emails that bypass traditional detection methods and fool even trained employees. Gone are the days of obvious spelling mistakes and broken English that made…
Read MoreHacking Campaign Has Breached Cisco Devices In US Government
Current Situation CISA released an emergency directive on Thursday targeting cyber threats against government networks. The directive orders federal agencies to take immediate action on compromised Cisco devices found across their systems. Hackers successfully breached firewalls used by multiple government organizations. These attacks targeted Cisco networking products that protect sensitive federal systems. The breaches represent…
Read MoreInside Scattered Spider’s Web: Why NYC Financial Institutions Must Strengthen Cybersecurity Posture Now
New York City’s financial institutions face a growing threat from Scattered Spider, a cybercriminal group that has significantly evolved its tactics since the FBI’s July 29, 2025 joint advisory. This sophisticated threat actor now deploys DragonForce ransomware alongside advanced social engineering techniques that specifically target large companies and their IT help desks. Financial firms are…
Read MoreRansomware and the Importance of Cybersecurity for Small Businesses: Lessons from the Recent Victoria’s Secret Attack
Ransomware attacks continue to disrupt businesses of all sizes, with recent headlines like last week’s attack on Victoria’s Secret proving that no organization is immune. For small businesses, the risks posed by cybercrime are particularly concerning, as limited resources can make it challenging to recover quickly from these incidents. Implementing a strong cybersecurity strategy is…
Read More