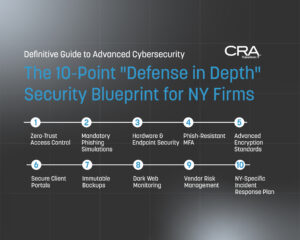
Advanced Cybersecurity for New York Law Firms: The Definitive Guide for Compliance & Protection in 2026
Introduction: The Cost of Complacency in the New York Legal…
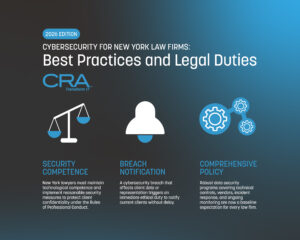
Cybersecurity for New York Law Firms: Best Practices – 2026 Edition
Cybersecurity Best Practices and Legal Duties for Law Offices in…
Best IT Support for Law Firms in NYC – 2026 Guide for Attorneys
A 2026 Guide to Choosing The Best IT Partner For…
Managed IT Services vs. In-House IT: Cost Comparison in NYC for 2026
Manhattan Cost Comparison 2026 Choosing between managed IT services and…
The 2026 NYC RIA Cybersecurity Guide: IT Security Requirements for Wealth Management
Cybersecurity as a Fiduciary Duty: Protecting HNW Assets in the…
NYDFS Part 500 Certification 2026: The Audit Defense Blueprint
The 2026 NYC Guide to ‘Insurance-Grade’ NYDFS Part 500 Certification…
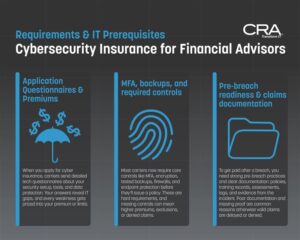
A Financial Advisor’s Guide To Cybersecurity Insurance in New York
NYDFS Part 500 Compliance Standards, IT Prerequisites, and Strategies to…
IT Requirements for FINRA Compliance in New York – (UPDATED For 2026)
Beyond Rule 4370: A Cybersecurity and Compliance Guide for Broker-Dealers …
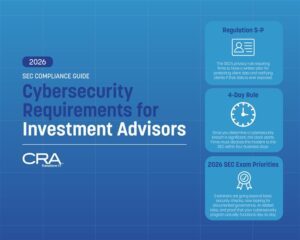
SEC Cybersecurity Requirements: Your 2026 Compliance Guide for Investment Advisors in New York
Investment advisors face a complex web of SEC cybersecurity requirements…
Computer Resources of America Earns Place on CRN’s Prestigious 2026 Tech Elite 250 List
The New York-Based Solution Provider Was Once Again Recognized Among…
Cybersecurity Is Patient Safety: Lessons from the Stryker Intune Wiper Event—and How Healthcare Can Build Resilience Now
A destructive wake‑up call for healthcare This week’s destructive attack…
What is IT Support? Dive Deeper with Insights from Our IT Support Blog
Join us as we delve into a myriad of topics essential for business continuation, including what IT support is, and how managed IT services, cloud computing, IT consulting, and IT security, among others, can integrate into your business strategy.
At CRA, we pride ourselves on offering insightful content tailored to specific industries, such as non-profit, education, healthcare, and technology. This strategic categorization ensures that our readers can easily find content relevant to their sector, providing targeted insights that can be directly applied to their unique IT challenges. Whether you're an IT professional, business owner, or simply curious about the technological landscape, our IT company blog is your one-stop destination for enriching your knowledge and staying ahead in the fast-paced world of IT.

Contact Us for Full-Service IT Support
We’re ready to make our IT support services work for you. When you want managed IT, cybersecurity for small businesses, or any of our other essential IT services, we’ve got you covered. Contact us today to get started with your free evaluation. As your company, we make your complete satisfaction with our services our number one priority.
"*" indicates required fields